Hackers of CypherCon - Season 2

Season 2
CypherCon 4.0

Episodes

A Kinesthetic Approach to Learning Encryption with Antoinette Stevens
Kinesthetic style, or tactile learning, means that some learn best by physically doing to fully learn and memorize a topic. Capture the flag competitions can be a way to understand security concepts with reading, understanding, applying and watching it in action. Creating a full multi-sensory learning experience to retain those concepts in memory for later.

More Than Tor: Shining a Light on Different Corners of the Dark Web with Benjamin Brown
When the terms Darknet or Dark Web are invoked, it is almost always in reference to the Tor network, but what about the other extant Darknet frameworks? In this talk Benjamin will expand the field of view to include frameworks such as Freenet, I2P, and OpenBazaar. He'll take a quick look at the origins and technical underpinnings of these Darknets as well as their actors and offerings.

The Magic of Forensic Artifacts Hiding in Plain Sight with Cindy Murphy
Digital forensics expert Cindy Murphy, M.Sc. will use this session to unpack the myths of digital forensics she uncovered since her career pivot from law enforcement to private digital forensics work. She will discuss how to navigate common myths and most importantly, how to keep moving forward in an ever-changing industry.

Spitting the Hook: Examining Phishing Bait with Joe Cicero
In this very informative panel, Joe Cicero examines phishing bait for enterprise protection. Subjects covered are: the red flag concept, identifying phishing email basics, examining headers, examining attachments and links. Additional topics covered are: the differences between a legit email, spam, marketing and phishing.

Phreaking for Fun and Profit with Brad Swanson
Brad talk's about phone phreaking back in the late 1980's, until the mid 1990's. He will cover what phreaking was, why it worked, and why it was done. Devices used, the theory behind them, and some entertaining stories about those devices are covered. He will cover the slew of 'secret' numbers that existed in the phone system and discuss the decline in phreaking with the newer versions of ESS.

Shifting Security Left with Chris Merkel
The shift to the cloud is making it more difficult for security teams to control what happens in their organizations and secure systems. The solution is more security tools, more security people, and ever-inventive ways to reign in your environment. We'll talk about how engineering automation to create a culture of empowerment, self-reliance and trust can result in better security outcomes.

Bug Bounty Law with Dr. Amit Elazari Bar On
Bug Bounties and Vulnerability Disclosure Program (VDP) are one of the fastest growing, most popular ways for companies to engage with the security research community and uncover unknown security vulnerabilities. This talk will explore how the law interacts with bug bounties, VDP, anti-hacking laws, bounty legalese myths, and contract standardization efforts widely adopted across the industry.

Automating Hashtopolis with Dustin Heywood
This talk will cover the basics of using the user-api to automate functions in Hashtopolis. Connecting to an HTP instance, creating hashlists, creating attacks, recovering plaintext, user creation and more will be covered.

Welcome Our New A.I. Overlords with Ed Skoudis
Amazing new A.I. based services from Amazon, Google, and Microsoft let organizations rely on automated technology to crawl through their cloud-based data to identify sensitive info, security weaknesses, and hacking attempts. In this talk, Ed will analyze security implications, ethical, business, and privacy issues they raise as cloud-based A.I. intertwines itself in our lives deeper every day.

Tracking an Adversary's Learning Curve with Edd Black
There are 2 camps of attackers: low skilled opportunists (script kiddies) and APT - Advanced Persistent Threats (funded organized crime, nation states). In between lurks a skilled persistent threat, capable of doing even more damage. These adversaries require human responders to identify, track, & oppose. Understand the constraints of the persistent threat, and you can learn to counter them.

Remote Wireless Pentesting with Eric Escobar & Matt Orme
Wireless pentesting typically requires physical proximity to a target which requires time, limited resources, and constant traveling. Eric & Matt have pioneered an inexpensive device to covertly perform wireless pentests anywhere on earth. In this talk, they'll discuss why they built it, how it works, and why they think it will revolutionize wireless pentesting.

Building a Cohesive Undergraduate Security Club with Ian Klatzco
The university security club had its ups and downs between boring meetings and inaccessibility to newcomers. It improved with a tighter meeting format, approachable 24-7 internal CTF, and internal documentation. There was better attendance, more people staying after meetings, and freshmen successfully completing projects with upperclassman mentorship. Interested? Learn more by watching this video.

Encryption, Silver Bullets & Holy Water with J. Wolfgang Goerlich
Werewolves attack, we have silver bullets. Vampires attack, we have holy water. Criminal hackers attack, we have encryption. The villains come and the heroes fight back. But too often, encryption is like water without the holy or bullets without the silver. The configuration is wrong or the code is incomplete. This talk will cover how and where to architect for encryption to get real protection.

Always Look a Gift (Trojan) Horse In the Mouth with James Arndt

Unhinging Security On the Buffalo Terastation NAS with Ian Sindermann

Decrypting the Mess that is Communication Security Negotiation with Jim Nitterauer

What are We Thinking Here? Rethinking Security with Jeff Man

Sorry About Your WAF with Johnny Xmas & Sam Crowther

What the World Needs Now is Ham, Sweet Ham with Jonathan Tomek

Spelunking the Bitcoin Blockchain with Josh Bressers

Thrift Shopping with your Data with Josh Frantz

Capture the Fail - Avoiding Pitfalls when running your C.T.F. with Kris & Chris Silvers

Anatomy of a Hot Wallet: Bitcoin at Scale with Matthew Werner

Don't Forget to Wipe with Michael Portera

What Happens when a Genome Database is Breached with Michelle Meas

Urban Foraging: Back to our Beginnings with Nick Wersel

Journey to Command Injection with Rick Ramgattie

Micro and Nano Segmentation with Russ From

A look at Historic Cons & their Transition to a Digital World with Stephanie Carruthers

Bet You Never Played an NES Game Like This with Vi Grey

The X-15 Rocket Plane, Flying the First Wings into Space with Michelle Evans
Recently Updated Shows
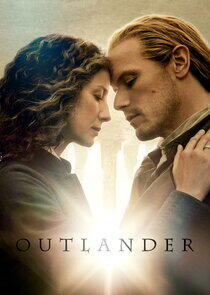
Outlander
Outlander follows the story of Claire Randall, a married combat nurse from 1945 who is mysteriously swept back in time to 1743, where she is immediately thrown into an unknown world where her life is threatened. When she is forced to marry Jamie, a chivalrous and romantic young Scottish warrior, a passionate affair is ignited that tears Claire's heart between two vastly different men in two irreconcilable lives.
The Outlander series, adapted from Diana Gabaldon's international best-selling books, spans the genres of romance, science fiction, history and adventure into one epic tale.

The Boys
In a world where superheroes embrace the darker side of their massive celebrity and fame, The Boys centres on a group of vigilantes known informally as "The Boys," who set out to take down corrupt superheroes with no more than blue collar grit and a willingness to fight dirty.

Monarch: Legacy of Monsters
After surviving Godzilla's attack on San Francisco, Cate is shaken yet again by a shocking secret. Amid monstrous threats, she embarks on a globetrotting adventure to learn the truth about her family—and the mysterious organization known as Monarch.

Fire Country
In Fire Country, seeking redemption and a shortened prison sentence, young convict Bode Donovan joins a firefighting program that returns him to his small Northern California hometown, where he and other inmates work alongside elite firefighters to extinguish massive blazes across the region.

Elsbeth
Elsbeth follows Elsbeth Tascioni, an astute but unconventional attorney who utilizes her singular point of view to make unique observations and corner brilliant criminals alongside the NYPD. After leaving her successful legal career in Chicago to tackle a new investigative role in New York City, Elsbeth finds herself jockeying with the toast of the NYPD, Captain C.W. Wagner, a charismatic and revered leader. Working alongside Elsbeth is Officer Kaya Blanke, a stoic and ethical officer who quickly develops an appreciation for Elsbeth's insightful and offbeat ways.